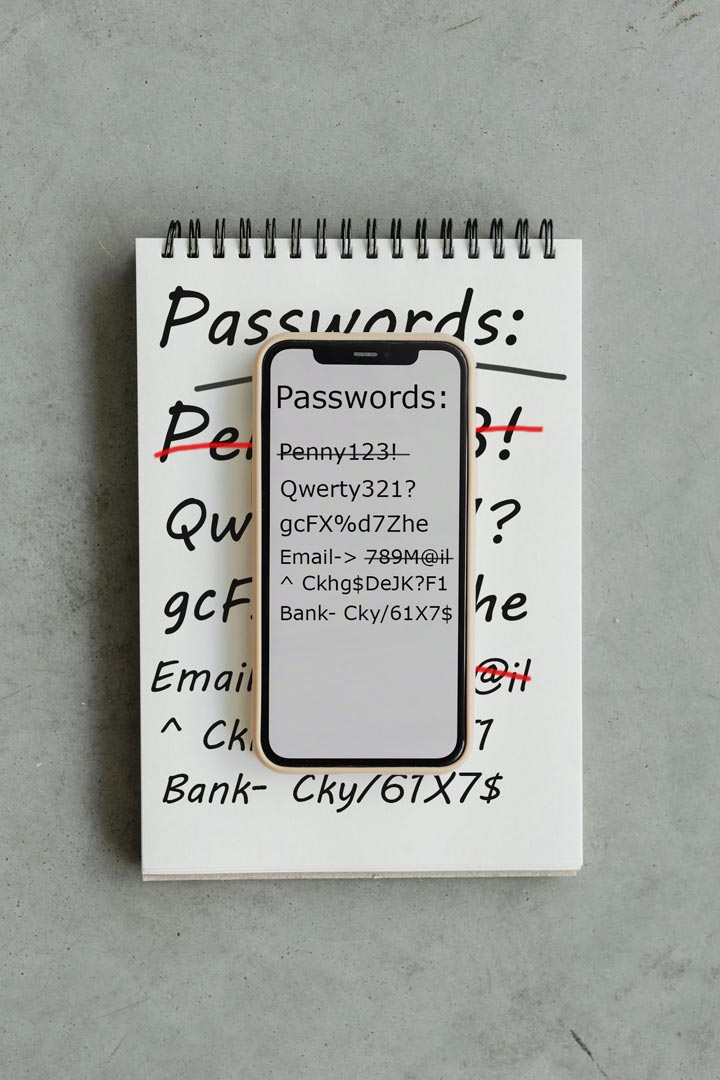
Good password management is no longer optional. Most of our personal and professional lives now exist online, and nearly every service we use depends on login credentials. Unfortunately, many of the habits people developed years ago like reusing passwords, writing them down in notebooks, or relying entirely on a single device, were never designed for the scale we operate today. As modern systems have become larger and more complex, the number of threats we face has also increased.
The good news is that improving your password security doesn’t require advanced technical knowledge. By adopting a dedicated password manager and using stronger password practices, you can dramatically reduce the risk of account compromise, identity theft, and the frustration of constantly resetting forgotten passwords.
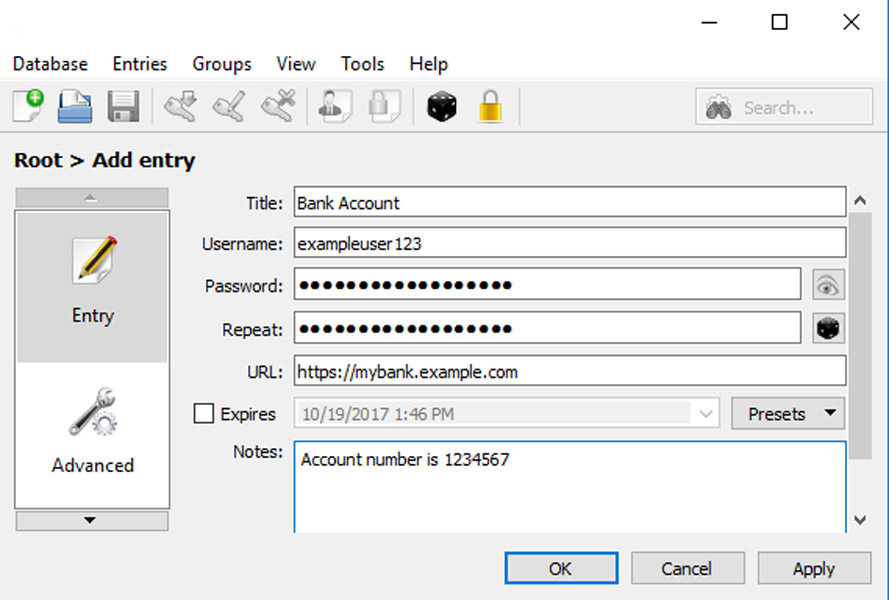
In this article we’ve covered some of the most common password habits and why they can create problems over time. In the next part of this series, we will look at several popular password managers and compare their features, security models, and ease of use. After that, we will walk through a step-by-step tutorial showing how to set up and migrate your existing passwords into one of the most recommended options.
While nobody enjoys spending time managing their passwords, a small investment of time now can save you from potentially significant problems later and make your digital life more secure for years to come.